Data Security
To protect the privacy of research participants and support data integrity, the GDC requires user authorization and authentication for:
- downloading controlled-access data
- submitting data to the GDC
To perform these functions, GDC users must first obtain appropriate authorization via dbGaP and then authenticate via eRA Commons. The GDC sets user permissions at the project level according to dbGaP authorizations.
See Data Access Processes and Tools to learn more about the difference between open-access and controlled-access data.
Authorization via dbGaP
Instructions for obtaining authorization via dbGaP are provided in Obtaining Access to Controlled Data and Obtaining Access to Submit Data.
Authentication via eRA Commons
The following authentication methods are supported by the GDC:
| GDC Tool | Authentication Method |
|---|---|
| GDC Data Portal | Log in using eRA Commons account |
| GDC Data Submission Portal | Log in using eRA Commons account |
| GDC Data Transfer Tool | Authentication Token |
| GDC API | Authentication Token |
Authentication Tokens
The GDC Data Transfer Tool and the GDC API use tokens for authentication. GDC authentication tokens are alphanumeric strings of characters like this one:
ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTOKEN-01234567890+AlPhAnUmErIcToKeN=0123456789-ALPHANUMERICTO
Logging into the GDC
To login to the GDC, users must click on the Login button on the top right of the GDC Website.
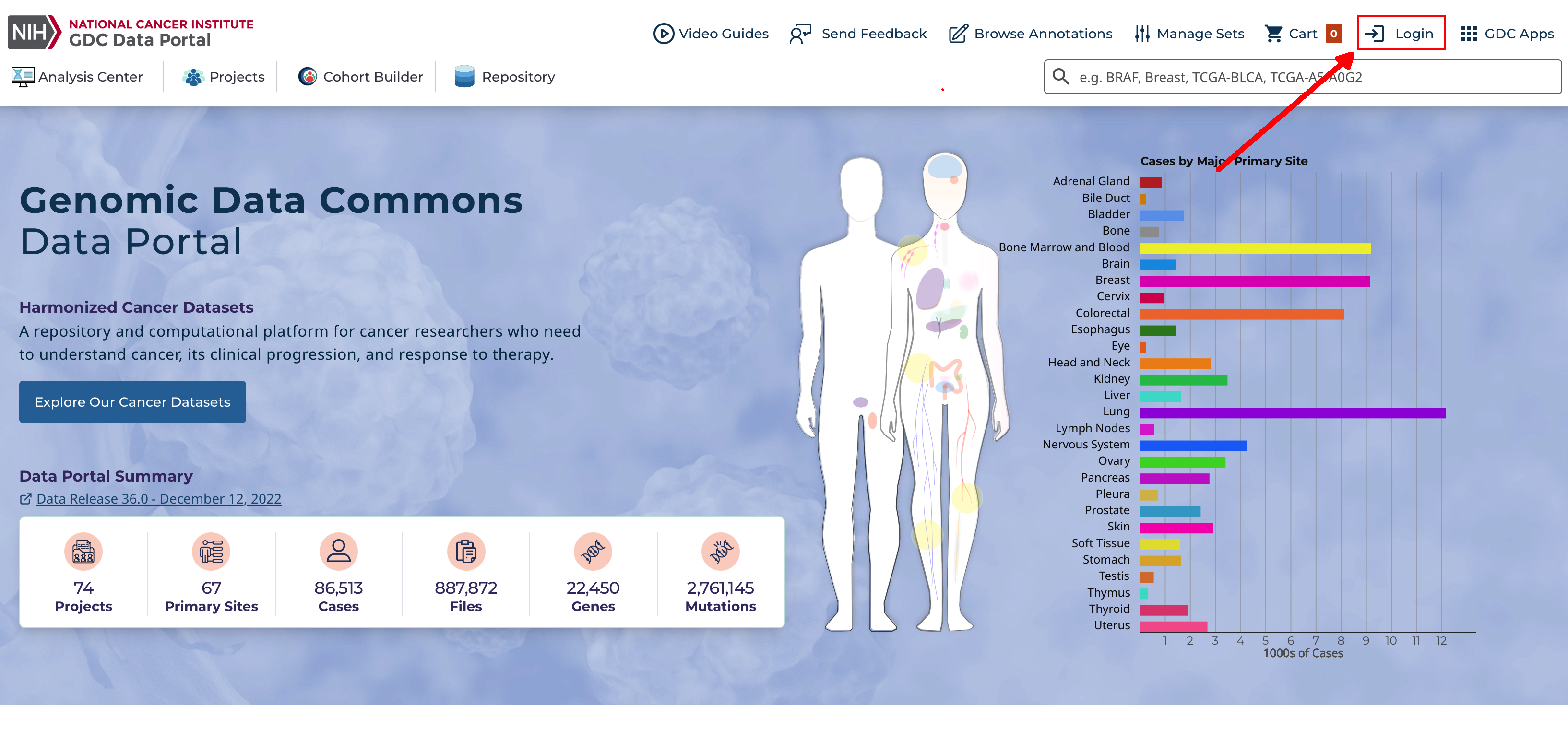
After clicking Login, users authenticate themselves using their eRA Commons login and password. If authentication is successful, the eRA Commons username will be displayed in the upper right corner of the screen, in place of the "Login" button.
Upon successful authentication, GDC Data Portal users can:
- See which controlled-access files they can access.
- Download controlled-access files directly from the GDC Data Portal.
- Download an authentication token for use with the GDC Data Transfer Tool or the GDC API.
- See controlled-access mutation data they can access.
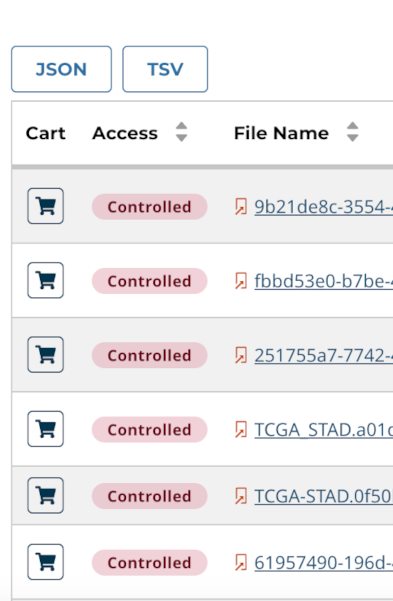
Controlled-access files are identified via their status in the Access Column:
The rest of this section describes controlled data access features of the GDC Data Portal available to authorized users. For more information about open and controlled-access data, and about obtaining access to controlled data, see Data Access Processes and Tools.
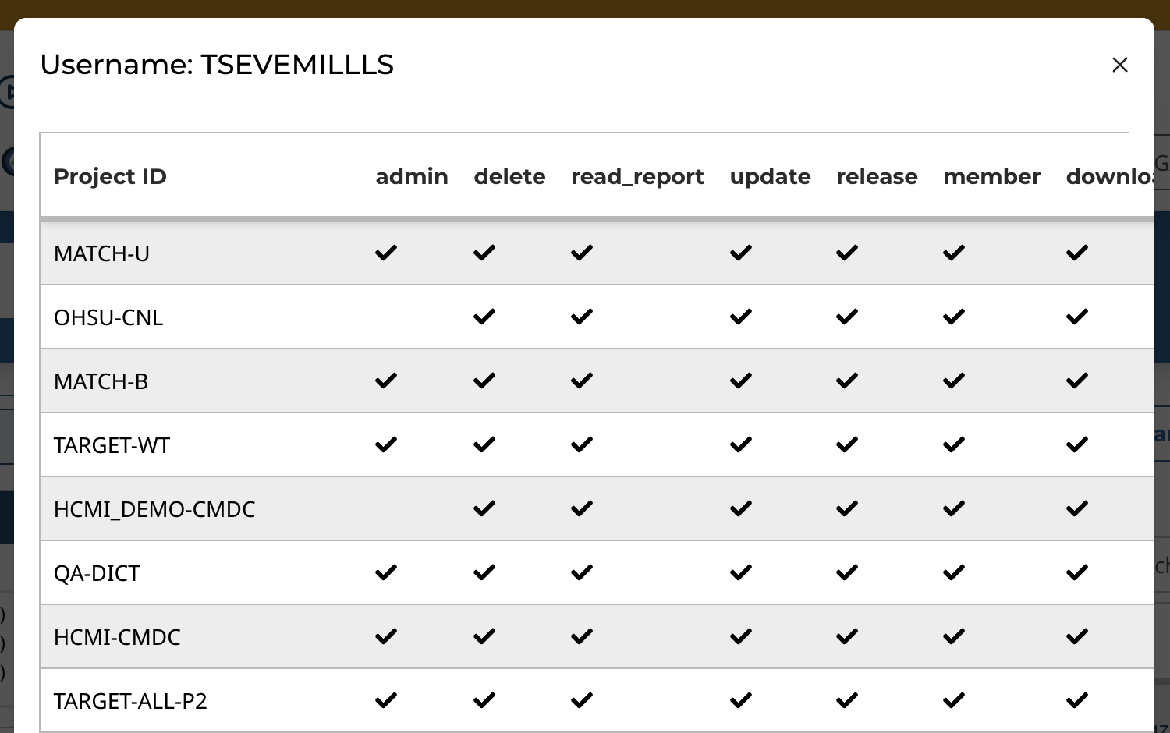
User Profile
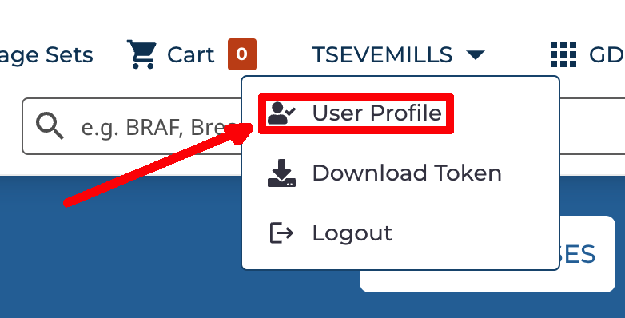
After logging into the GDC Portal, users can view which projects they have access to by clicking the User Profile section in the dropdown menu in the top corner of the screen.
Clicking this button shows the list of projects.
GDC Authentication Tokens
The GDC Data Portal provides authentication tokens for use with the GDC Data Transfer Tool or the GDC API. To download a token:
- Log into the GDC using your eRA Commons credentials.
- Click the username in the top right corner of the screen.
- Select the "Download token" option.
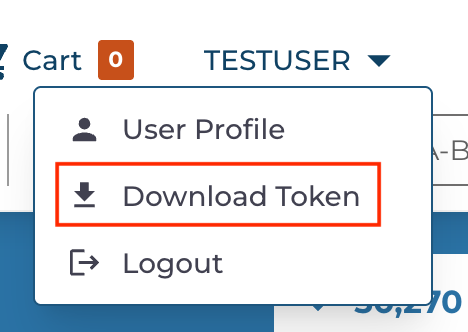
A new token is generated each time the Download Token button is clicked.
For more information about authentication tokens, see Data Security.
Note: The authentication token should be kept in a secure location, as it allows access to all data accessible by the associated user account.
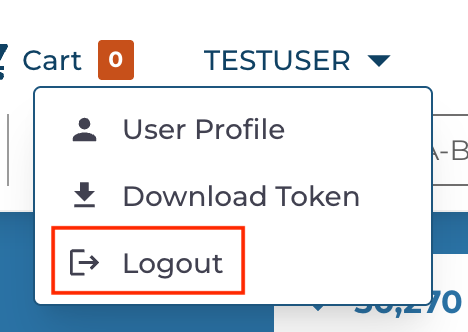
Logging Out
To log out of the GDC, click the username in the top right corner of the screen, and select the Logout option.
Obtaining A Token
Users can obtain authentication tokens from the GDC Data Portal and the GDC Data Submission Portal. See the GDC Data Submission Portal User's Guide for instructions.
Token Expiration
Tokens are valid for 30 days from the time of issue. Any request to the GDC API that uses an expired token will result in an error.
Tokens can be replaced at any time by downloading a new token, which will be valid for another 30 days.
Checking User Permissions
Users can view the permissions granted to them by the GDC system as follows:
- Log into the GDC Data Portal or the GDC Data Submission Portal using your eRA Commons account.
- Open the URL
https://portal.gdc.cancer.gov/auth/userto see a JSON object that describes user permissions.